Explosive Study Reveals Dark Side of Search Engines
Have you ever wondered if search engines are truly reliable sources of information? Brace yourself, because a groundbreaking study has just uncovered a dark side that will make you question everything.
This explosive revelation sheds light on the hidden truths behind search engine algorithms and the influence of highly-optimized content on the integrity of search results. But that's not all – the study also reveals the prevalence of biased product reviews and the promotion of conspiracy theories.
Get ready to have your perception shattered as we unveil the shocking findings and explore the implications they have on the information you trust.
Key Takeaways
- Search engines have significant problems with highly-optimized (affiliate) content, particularly in product reviews where websites prioritize selling products over providing unbiased information.
- Google has made specific improvements to address these issues and performs better than other search engines, although there is still room for enhancement in text quality.
- Bing and DuckDuckGo consistently displayed conspiracy-promoting results and links to conspiracy-dedicated websites, while Google ranked lower in terms of promoting conspiracy theories.
- Affiliate marketing significantly affects search results, with most results using affiliate marketing and compromising the quality and usefulness of the information provided.
Study Findings on Search Engine Problems

The study findings on search engine problems reveal significant issues with the quality of search engine results, particularly in relation to highly-optimized (affiliate) content. Search engine optimization challenges and the impact of biased product reviews are key concerns.
A year-long monitoring of Google, Bing, and DuckDuckGo on 7,392 product review queries showed that higher-ranked pages were more optimized and monetized with affiliate marketing. These pages also displayed signs of lower text quality. The study highlights the prevalence of websites focused on selling products rather than providing unbiased information.
Google has made efforts to address these issues, and while it performs better than other search engines, there's still room for improvement in text quality. Bing and DuckDuckGo consistently displayed conspiracy-promoting results and links to conspiracy-dedicated websites, while Google ranked them lower.
Affiliate marketing is a common practice in search results, compromising the usefulness of the information provided. AI's impact on search results quality is also a concern, as it blurs the line between benign content and spam.
Google's Improvement Efforts
Google has taken steps to address the issues highlighted in the study on search engine problems, focusing on improving the quality of search results. Their updates have had a noticeable, albeit short-lived, effect on reducing affiliate spam. However, there are still areas for further improvement, particularly in text quality across all search engines. To illustrate the effectiveness of Google's updates, let's look at a comparison of search engine results quality using a table:
| Search Engine | Effectiveness of Updates | Areas for Further Improvement |
|---|---|---|
| Noticeable improvement | Text quality | |
| Bing | Less effective | Conspiracy theories |
| DuckDuckGo | Less effective | Conspiracy theories |
As shown in the table, Google has performed better than other search engines and has made strides in addressing the issues identified in the study. However, there is still room for improvement, particularly in enhancing text quality.
Comparison of Conspiracy Theory Promotion

When comparing the promotion of conspiracy theories across different search engines, it's evident that Bing and DuckDuckGo consistently display more results and links to conspiracy-dedicated websites. This has significant implications for the influence of conspiracy theories on public opinion and the role of search engines in shaping societal beliefs.
- Bing and DuckDuckGo's promotion of conspiracy theories can contribute to the spread and normalization of these ideas, potentially leading to the distortion of public perception.
- The availability of conspiracy theory websites on these search engines allows individuals to easily access and consume such content, reinforcing their beliefs and potentially deepening their involvement in conspiracy communities.
- The prominence of conspiracy theories in search results can create an echo chamber effect, where individuals are exposed to a limited range of perspectives, further reinforcing their existing beliefs and potentially isolating them from alternative viewpoints.
It is crucial to recognize the influence that search engines have on public opinion and take steps to ensure the responsible promotion of information that's accurate, unbiased, and reliable.
Influence of Affiliate Marketing on Search Results
As we delve into the influence of affiliate marketing on search results, it's important to understand the impact this marketing strategy has on the quality and reliability of the information presented to users.
Affiliate marketing is widely used in search engine results, with the majority of search results incorporating affiliate links. However, its effectiveness in providing valuable and trustworthy content is questionable. Affiliate sites prioritize driving clicks and generating revenue, often compromising the quality of the information provided. This compromises the usefulness and accuracy of the search results.
Additionally, the monetization of content through affiliate marketing often leads to a decrease in content complexity, as affiliate marketers prioritize attracting clicks rather than focusing on producing high-quality and comprehensive content. Therefore, the impact of monetization on content quality is a significant concern when considering the influence of affiliate marketing on search results.
AI's Impact on Search Results Quality
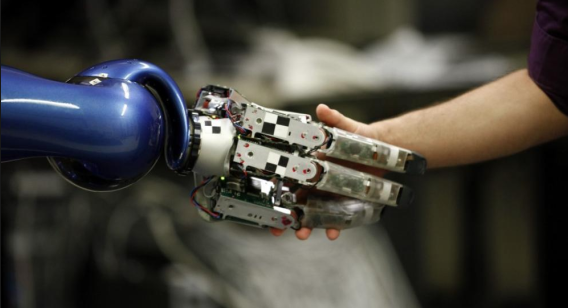
AI's impact on search results quality is a growing concern due to its potential to lower text quality, increase spam, and compromise the accuracy and usefulness of the information provided.
This has several implications for the user experience:
- Decreased text quality: AI's writing component is sub-par, leading to lower quality content. This can make it harder for users to find reliable and relevant information.
- Increased spam: AI enables the creation of large amounts of acceptable content quickly and at a lower cost. This opens the door for spam tactics, flooding search results with irrelevant and low-quality information.
- Challenge in combating AI-powered spam: AI-powered spam campaigns are difficult to detect and combat. Search engines need to adapt their algorithms to stay ahead of these tactics and maintain the quality of search results.
Addressing these challenges is crucial to ensure that users can trust the information they find and have a positive search experience.
Frequently Asked Questions
How Do Search Engines Determine the Ranking of Product Review Pages?
Search engine algorithms determine the ranking of product review pages based on various ranking factors. These factors include relevance, user experience, authority, and quality of content. The goal is to provide users with the most helpful and reliable information.
What Specific Improvements Has Google Made to Address the Issues Highlighted in the Study?
Google has made specific improvements to address the issues highlighted in the study. Search engine algorithms have been updated to reduce affiliate spam. However, further enhancements are needed to improve overall text quality.
How Do Bing and Duckduckgo Compare to Google in Terms of Promoting Conspiracy Theories?
Bing and DuckDuckGo promote more conspiracy theories compared to Google. They consistently display conspiracy-promoting results and links to dedicated websites. Google includes some untrustworthy sites but ranks them lower.
What Percentage of Product Reviews on the Web Use Affiliate Marketing?
Affiliate marketing is prevalent in most product reviews on the web. This impacts the objectivity of reviews, as they prioritize driving clicks and making money, compromising the quality of unbiased information provided.
How Can Search Engines Adapt Their Algorithms to Combat Spam Tactics Facilitated by Ai?
Search engines can combat spam tactics facilitated by AI by implementing AI-based techniques for spam detection. Additionally, they can utilize user feedback to improve algorithms and identify and penalize websites that engage in spamming practices.
Conclusion
In conclusion, the study's findings on the dark side of search engines reveal the alarming extent to which highly-optimized and monetized content compromises the objectivity and reliability of search engine results.
For example, imagine searching for a product review and finding the top-ranked page filled with biased information, solely aimed at promoting sales.
This study highlights the urgent need for search engine improvement to ensure the integrity of online information and protect users from misleading and manipulated content.







































 Shared hosting is the rental of a small space on the server, which also houses other sites. Managed by the host, you don’t have to worry about technical and security aspects. To pick a good host, it is necessary to look at its “uptime,” i.e., the percentage of time the machine is inaccessible; the good servers are between 99 and 100%. The major disadvantage of this solution is its lack of flexibility: you are dependent on the server configuration, you cannot install other options, and your resources are limited.
Shared hosting is the rental of a small space on the server, which also houses other sites. Managed by the host, you don’t have to worry about technical and security aspects. To pick a good host, it is necessary to look at its “uptime,” i.e., the percentage of time the machine is inaccessible; the good servers are between 99 and 100%. The major disadvantage of this solution is its lack of flexibility: you are dependent on the server configuration, you cannot install other options, and your resources are limited.

 MacRumors’ bloodhounds spotted an internal memo from Virgin Mobile employees. According to this memo, iPhone 8 and 8 Plus (Product) Red are in the cartons, and the announcement of these red versions could be imminent since the site indicates that these red iPhone should be officialized this Monday, April 9. The operator’s memo does not refer to iPhone X, so we can imagine that Apple’s flagship will not be part of this initiative.
MacRumors’ bloodhounds spotted an internal memo from Virgin Mobile employees. According to this memo, iPhone 8 and 8 Plus (Product) Red are in the cartons, and the announcement of these red versions could be imminent since the site indicates that these red iPhone should be officialized this Monday, April 9. The operator’s memo does not refer to iPhone X, so we can imagine that Apple’s flagship will not be part of this initiative.
 patible. They each take place twice a year, around March and September. In the wake of the Windows 10 Fall Creators Update released in early October, the next Windows 10 upgrade (the Spring Creators Update) should, therefore, be launched by the end of the month. Microsoft has already announced what should be its primary innovations:
patible. They each take place twice a year, around March and September. In the wake of the Windows 10 Fall Creators Update released in early October, the next Windows 10 upgrade (the Spring Creators Update) should, therefore, be launched by the end of the month. Microsoft has already announced what should be its primary innovations:
 With Gemini 2, you are going to be able to scour through your entire Mac using its algorithm, and it’s shockingly simple user interface. By simply pressing a button, you will be able to allow Gemini 2 to locate all of the duplicates it finds in your storage. It will then present you with the results which you can either instantly delete to free up valuable storage space, or you can go through it and see whether or not you might want to keep some of the duplicates it found. While you might not need to use a software like this all of the time, it can be a great maintenance tool to use once a month to free up valuable storage space on your internal hard drive.
With Gemini 2, you are going to be able to scour through your entire Mac using its algorithm, and it’s shockingly simple user interface. By simply pressing a button, you will be able to allow Gemini 2 to locate all of the duplicates it finds in your storage. It will then present you with the results which you can either instantly delete to free up valuable storage space, or you can go through it and see whether or not you might want to keep some of the duplicates it found. While you might not need to use a software like this all of the time, it can be a great maintenance tool to use once a month to free up valuable storage space on your internal hard drive.
 Now, publishing “identical or substantially similar” content from multiple accounts is prohibited, and can no longer be an option in Twitter programs. This rule applies to both simultaneous and scheduled publication.
Now, publishing “identical or substantially similar” content from multiple accounts is prohibited, and can no longer be an option in Twitter programs. This rule applies to both simultaneous and scheduled publication. The TweetDeck application will be modified to match these new rules: its users will no longer be able to tweet, retweet, like or track someone from different accounts. The applications and services that allow such actions must be modified by March 23, 2018, under penalty of suspension of the applications or accounts concerned.
The TweetDeck application will be modified to match these new rules: its users will no longer be able to tweet, retweet, like or track someone from different accounts. The applications and services that allow such actions must be modified by March 23, 2018, under penalty of suspension of the applications or accounts concerned.
 As far as the principle is concerned, the ECU constantly receives information from the various sensors on the vehicle. It has a correct value range, beyond this range or in the total absence of a signal, it considers the element concerned to be out of service. This causes the diagnostic indicator light to illuminate. It can also compare the information of the different sensors and see an anomaly.
As far as the principle is concerned, the ECU constantly receives information from the various sensors on the vehicle. It has a correct value range, beyond this range or in the total absence of a signal, it considers the element concerned to be out of service. This causes the diagnostic indicator light to illuminate. It can also compare the information of the different sensors and see an anomaly. The ideal is the suitcase manufacturer but it is very difficult to get one. Nevertheless, there are a multitude of universal suitcases for cars on the market. You can choose between purchasing the USB cabling or connecting it to a PC on which you have installed an interface software, or buying a portable box directly to read the faulty codes.
The ideal is the suitcase manufacturer but it is very difficult to get one. Nevertheless, there are a multitude of universal suitcases for cars on the market. You can choose between purchasing the USB cabling or connecting it to a PC on which you have installed an interface software, or buying a portable box directly to read the faulty codes.
 One of these features is aimed at redirects that automatically return the user to another page. According to Google, these redirections do not usually come from the creator of the page, but from the third party, elements integrated by the latter.
One of these features is aimed at redirects that automatically return the user to another page. According to Google, these redirections do not usually come from the creator of the page, but from the third party, elements integrated by the latter.
 The Internet and video games are now part of our daily lives, which does not prevent them from being regularly the focus of controversy. They are readily credited with having a negative influence on the new generations.
The Internet and video games are now part of our daily lives, which does not prevent them from being regularly the focus of controversy. They are readily credited with having a negative influence on the new generations. The Internet offers opportunities and accessibility to a wide variety of content. Combined with the ability to remain anonymous behind the screen, these new uses are changing our online media and behaviors.
The Internet offers opportunities and accessibility to a wide variety of content. Combined with the ability to remain anonymous behind the screen, these new uses are changing our online media and behaviors.
 An electric kettle is easy to wash: a mixture of malt vinegar and water, which is brought to the boil and with which the resistance is involved, is used. Alternatively, put a coke-based soda in the kettle and run the kettle. It will be like new!
An electric kettle is easy to wash: a mixture of malt vinegar and water, which is brought to the boil and with which the resistance is involved, is used. Alternatively, put a coke-based soda in the kettle and run the kettle. It will be like new!


 When IT is used on a regular basis, it may be necessary to ensure that all of your systems are as well protected as they can be. Up to ten percent of companies have not made any attempts to upgrade their security recently and this could pose a real threat to their business.
When IT is used on a regular basis, it may be necessary to ensure that all of your systems are as well protected as they can be. Up to ten percent of companies have not made any attempts to upgrade their security recently and this could pose a real threat to their business.

 Those characters that are newer to the franchise are no less popular despite their lack of intrinsic value. Characters such as Ahsoka Tano, Anakin Skywalker, and even General Grievous are hard to find at times, as their popularity is rivalled by only a few.
Those characters that are newer to the franchise are no less popular despite their lack of intrinsic value. Characters such as Ahsoka Tano, Anakin Skywalker, and even General Grievous are hard to find at times, as their popularity is rivalled by only a few.